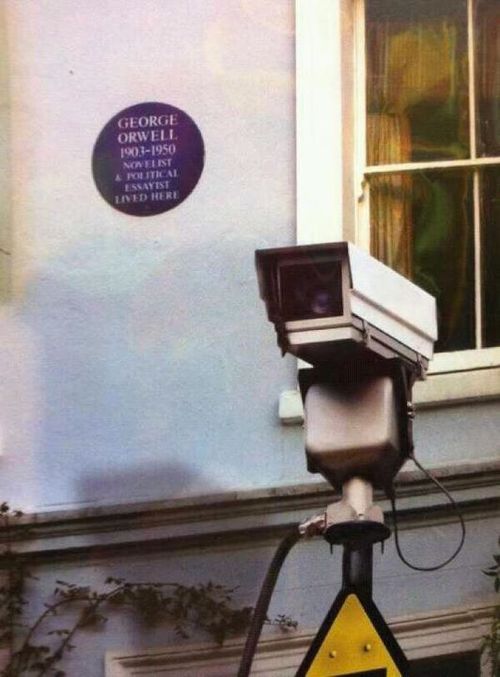
One photo = 1k word Soliloquy
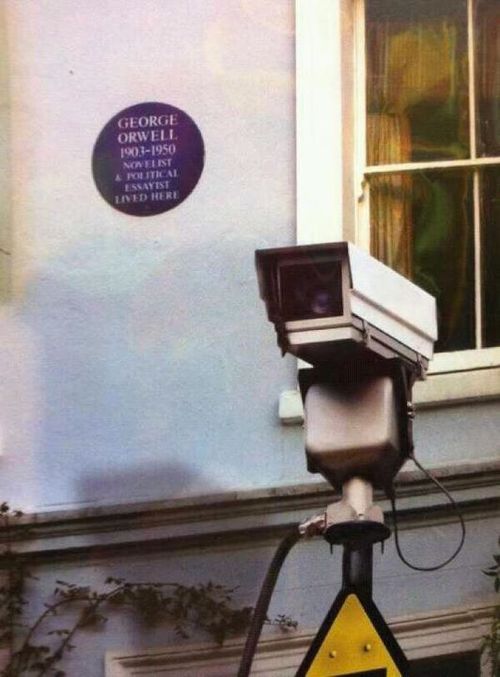
One photo = 1k word Soliloquy
A scrimmage in a Border Station
A canter down some dark defile
Two thousand pounds of education
Drops to a ten-rupee jezail
http://i.imgur.com/IPT1uLH.jpg
As the UK chattering politicians post-Woolwich push for the "snooper's charter" bill to be reintroduced Denmark reports data collection is not that useful:Link:http://techpresident.com/news/wegov/...igital-privacy...five years of extensive Internet surveillance have proven to be of almost no use to the police. Session logging has caused serious practical problems....The implementation of session logging proved to be unusable to the police; this became clear the first time they tried to use [the data] as part of a criminal investigation
Back to the UK debate. An IT expert's thoughts:http://www.eradar.eu/2013/05/communi...t-opportunism/
'Naked Citizens' is a short twenty-five minute film on surveillance; it is not obsessed with:It starts with a good explanation of 'smart' CCTV identifying aberrant behaviour, but then becomes more strident. Anyway some interesting concepts are explained, notably suspicion, anonymity and privacy...With one camera for every 14 people in London...
Link:http://www.journey.webbler.co.uk/?lid=65226&bid=2
davidbfpo
An example of vulnerability and in Syria, so no surprises that many sources have disappeared into the regime's care:http://www.cjr.org/feature/the_spy_w...c.php?page=all
davidbfpo
An interesting and quite sad link with lots of further leads and reads.
After reading quite a bit about the latest events and trying to piece most of it into a big picture I had to note once again the deep irony of the whole story. The sheer size of the dragnet, and its depth needed a greatly increased the number of people working on secret stuff. The fear to fail to connect the dots has seemingly increased the amount of sharing and more people know more about the national efforts. The gigantic scope and reach of certain programs, especially those involving your average citizien have increased the danger of employing people who might feel it morally justified to whistleblow.
If that happens the public echo might be big indeed and it can indeed seriously harm directly and indirectly the most important, the true key interests of a nation. At least some sources are saying that terrorist groups have changed their comm. patters and that certain methods will be much harder to pull off. While there are certainly political games involved there should be a certain amount of truth in those informations. So if the fight against terrorism has indeed been the main goal of those various efforts then the NSA&Co might have scored an own goal in that area as well.
Last edited by Firn; 07-01-2013 at 09:32 PM.
... "We need officers capable of following systematically the path of logical argument to its conclusion, with disciplined intellect, strong in character and nerve to execute what the intellect dictates"
General Ludwig Beck (1880-1944);
Speech at the Kriegsakademie, 1935
I know many Americans have a strange regard, if not dislike for their postal service and it's inefficiencies - so they may think this odd:Link:http://www.nytimes.com/2013/07/04/us...pagewanted=all..the Mail Isolation Control and Tracking program, in which Postal Service computers photograph the exterior of every piece of paper mail that is processed in the United States about 160 billion pieces last year. It is not known how long the government saves the images.
That must be some computer database, even if only retaining the photos for thirty days.
davidbfpo
So when the US spooks want 'everything' they really want every metadata at least from US citiziens. More, if possible from the rest of the world.
In this case it seems as if the methods of the digital age have been brought into the old analog world. Legally the path has been the reverse. Whatever floats the boats and is possible seems to get done with the legal bounderies getting streched and streched or even completely removed...“In the past, mail covers were used when you had a reason to suspect someone of a crime,” said Mark D. Rasch, the former director of the Justice Department’s computer crime unit, who worked on several fraud cases using mail covers. “Now it seems to be ‘Let’s record everyone’s mail so in the future we might go back and see who you were communicating with.’ Essentially you’ve added mail covers on millions of Americans.”
Bruce Schneier, a computer security expert and an author, said whether it was a postal worker taking down information or a computer taking images, the program was still an invasion of privacy.
“Basically they are doing the same thing as the other programs, collecting the information on the outside of your mail, the metadata, if you will, of names, addresses, return addresses and postmark locations, which gives the government a pretty good map of your contacts, even if they aren’t reading the contents,” he said.
In such days it certainly feels like that the terrorists did indeed score some important victories against key and noble ideas of the Western World. And once again it seems that the scale of the tracking efforts opens the door for highly questionable abuses which pushes the whole thing into the spotlight and alerts also the valid targets. Imperial intelligence overstrech.Law enforcement officials need warrants to open the mail, although President George W. Bush asserted in a signing statement in 2007 that the federal government had the authority to open mail without warrants in emergencies or foreign intelligence cases.
Last edited by Firn; 07-03-2013 at 09:24 PM.
... "We need officers capable of following systematically the path of logical argument to its conclusion, with disciplined intellect, strong in character and nerve to execute what the intellect dictates"
General Ludwig Beck (1880-1944);
Speech at the Kriegsakademie, 1935
Petabytes (Wiki)
A billion 1MB scans = 1 petabyte; so, 160 billion scans per year at 1MB per scan = 160 petabytes. Hitachi was marketing 32 petabytes of rack storage in 2004 (BBC).1000 kB kilobyte
1000^2 MB megabyte
1000^3 GB gigabyte
1000^4 TB terabyte
1000^5 PB petabyte
1000^6 EB exabyte
1000^7 ZB zettabyte
1000^8 YB yottabyte
The Bluffdale UT database (easily expanded at ~$2billion per site) could take us into the zetta and yotta storage ranges (UK Guardian).
The USPS scans (@1MB per scan; a pure WAG) works out to ~ 1/2 petabyte (500 terabytes) per day - or 25 minutes of Bluffdale's daily capacity - IF Binney is in the correct order of magnitude; and if my math done in head is correct.William Binney, a mathematician who worked at the NSA for almost 40 years and helped automate its worldwide eavesdropping, said Utah's computers could store data at the rate of 20 terabytes – the equivalent of the Library of Congress – per minute. "Technically it's not that complicated. You just need to work out an indexing scheme to order it."
I believe all of this is due to the political response to the perceived demand by the American public for absolute security. Others will easily migrate to varied conspiracy theories. I believe it depends on whom we elect; and on whom they appoint. Others will disagree.
One can spend an interesting hour plus, watching William Binney on Youtube, NSA whistleblower William Binney Keynote at HOPE Number Nine (2012). Note the picture of the British sheep about two minutes into the video.
Regards
Mike
Last edited by jmm99; 07-03-2013 at 09:54 PM.
Actually the article's full title is 'NSA and GCHQ: the flawed psychology of government mass surveillance' and yes it is in The Guardian. The sub-title is probably more telling:Link:http://www.theguardian.com/science/h...nce?CMP=twt_guResearch shows that indiscriminate monitoring fosters distrust, conformity and mediocrity
I am uncertain about the science, but it certainly fits in here!
davidbfpo
Bookmarks